In the rapidly evolving world of cybersecurity, grasping how cyber attacks unfold is essential for organizations, businesses, and individuals to stay protected. The Cyber Kill Chain framework, first introduced by Lockheed Martin in 2011, offers a structured approach to dissecting and defending against advanced cyber threats. This in-depth guide draws from the groundbreaking paper “Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains” by Eric M. Hutchins, Michael J. Cloppert, and Rohan M. Amin. By breaking down cyber attacks into seven key stages, security teams can pinpoint vulnerabilities, implement layered defenses, and disrupt threats before they cause irreparable damage.
Whether you’re a cybersecurity analyst, IT professional, or executive concerned about data breaches and ransomware, understanding the Cyber Kill Chain can significantly bolster your threat intelligence, incident response, and overall cybersecurity strategy. In 2025, with the rise of AI-enhanced attacks and state-sponsored cyber operations, this model remains more relevant than ever. Let’s explore its stages, real-world applications, and how it integrates with modern tools.
The Evolution of Cyber Attacks: From Hobbyist Hacks to Sophisticated Operations
Back in the 1990s, cyber attacks were often dismissed as playful experiments by tech-savvy individuals. Fast forward to today, and they’ve transformed into highly organized endeavors driven by criminal syndicates, nation-states, and hacktivists using methodical, business-like processes. Inspired by military kill chain concepts, the Cyber Kill Chain treats intrusions as a series of interconnected milestones. While not every attack follows a strict linear progression—stages can overlap or loop—the framework’s core principle is that breaking any link in the chain can neutralize the entire threat.
Rooted in real-world adversary analysis, as outlined in Lockheed Martin’s 2011 paper, this model promotes intelligence-driven defenses to combat advanced persistent threats (APTs). In 2025, with cyber threats incorporating AI for automation and evasion, the Cyber Kill Chain continues to serve as a foundational tool, often complemented by frameworks like MITRE ATT&CK for more granular tactic mapping.

The Seven Stages of the Cyber Kill Chain Explained
The Cyber Kill Chain delineates seven phases: Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control, and Actions on Objectives. Below, we delve into each stage with practical examples, defensive tips, and insights updated for 2025’s threat landscape.
1. Reconnaissance: Gathering Intelligence on Targets
This initial phase mirrors traditional spying, where attackers scout for valuable targets by collecting data on IP addresses, domains, employee details, and exposed systems. For enterprises, it often begins with publicly available information from websites or social media, followed by IP sweeps to identify active hosts and port scans to uncover open ports, software versions, and potential weaknesses.
In today’s environment, attackers leverage botnets—vast networks of compromised devices—for automated, large-scale scanning. Defenders can counter this with network monitoring tools, honeypots to detect probes, and threat intelligence feeds. For instance, in recent state-linked attacks, such as the Algeria-Morocco cyber incident in April 2025, reconnaissance likely involved mapping government networks before data leaks.
2. Weaponization: Building Customized Exploits
Here, adversaries convert known vulnerabilities into weaponized payloads, tailoring malware to specific targets like a particular OS version or application. In the commoditized cybercrime market of 2025, attackers frequently buy ready-made exploits from dark web developers rather than coding from scratch, integrating them into automated platforms for efficiency.
The emphasis is on scalability and stealth, often incorporating AI to evade detection. Organizations can mitigate risks through regular vulnerability assessments and patch management. A prime example is the CL0P-linked hackers’ campaigns in September 2025, where pre-weaponized tools targeted email systems for mass exploitation.
3. Delivery: Infiltrating the Target Environment
Delivery focuses on smuggling the payload into the victim’s network. Common tactics include phishing emails with malicious attachments (e.g., PDFs or Office files), drive-by downloads from compromised websites, or exploiting stolen credentials for direct access.
Physical vectors like infected USB drives remain effective for air-gapped systems, while advanced attacks may use supply chain compromises. In 2025, with rising DDoS and ransomware threats, multi-vector deliveries are common. The Bragg Gaming Group breach in August 2025 illustrated this, where hackers accessed internal systems via initial delivery methods. Defenses include email gateways, web filters, and multi-factor authentication.
4. Exploitation: Activating the Payload
Exploitation triggers the payload, capitalizing on flaws in software, protocols, or human error. This could happen when a user opens an infected file, visits a malicious site exploiting browser vulnerabilities, or when attackers use credential stuffing on exposed services.
This stage automates much of the compromise, bridging delivery and persistence. With zero-day exploits on the rise in 2025, endpoint detection and response (EDR) tools are crucial. The Sepah Bank attack in June 2025 likely involved exploitation of financial software vulnerabilities amid geopolitical tensions.
5. Installation: Establishing a Foothold
Once inside, the payload installs itself in memory or on disk, often adding persistence mechanisms like Windows registry keys to survive reboots. This transforms the system into a zombie, ready for further commands.
Backdoors or remote access trojans (RATs) are commonly installed. To combat this, use application whitelisting and behavioral monitoring. In the GitHub “s1ngularity” attack affecting over 2,000 accounts in September 2025, installation allowed persistent malware deployment.
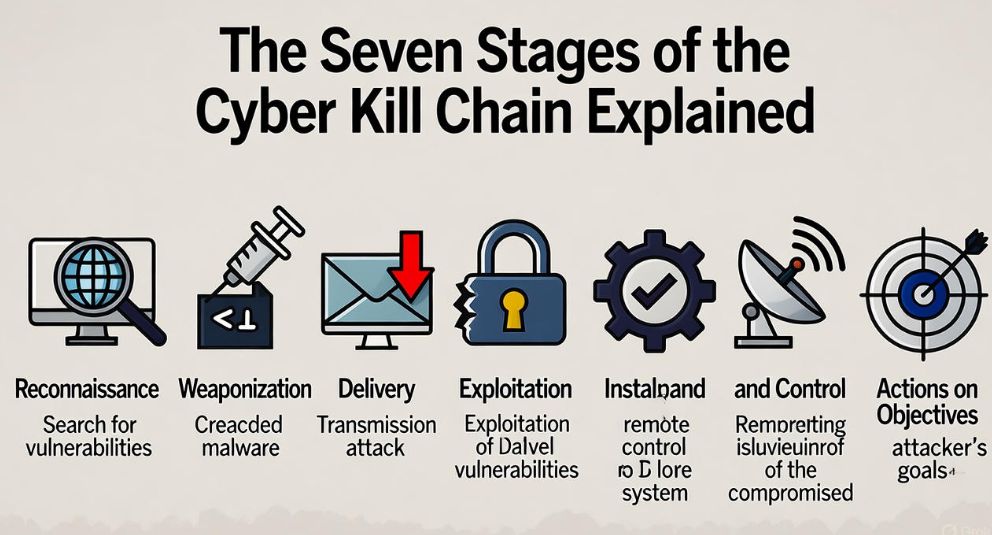
6. Command and Control (C2): Orchestrating the Attack
The infected system “phones home” to a C2 server, registering for instructions like file exfiltration or lateral movement. C2 channels often use domain generation algorithms (DGAs) to rotate addresses and avoid blacklisting.
In 2025, AI-driven C2 evasion is prevalent, making anomaly detection vital. Network segmentation and traffic analysis can disrupt this phase.
7. Actions on Objectives: Executing the End Goal
The climax involves achieving the attacker’s aim, such as stealing data, encrypting files for ransomware, or disrupting operations. Motivations range from financial gain (cybercriminals) to espionage (state actors) or activism.
This stage causes tangible harm, emphasizing early intervention. Recent examples include the Darktrace report on AI-adopted threats in the first half of 2025, where actions led to widespread data breaches.
Applying the Cyber Kill Chain in Real-World Scenarios
Organizations can map defenses across the chain using firewalls, intrusion prevention systems (IPS), and SIEM tools. As recommended in the original paper, analyzing past incidents helps develop detect-deny-disrupt-deceive strategies. For example, vulnerability scanning thwarts reconnaissance, while user awareness training reduces delivery success.
In 2025, integrate AI analytics for predictive threat hunting. Consider recent breaches like the CL0P email campaigns or Bragg Gaming intrusion—these often start with reconnaissance and delivery but can be halted at exploitation with robust EDR.
Conclusion: Adapting the Cyber Kill Chain for Future Threats
The Cyber Kill Chain endures as a cornerstone of cybersecurity, enabling proactive defenses against intricate attacks. As threats evolve—incorporating AI and targeting critical infrastructure—pairing it with MITRE ATT&CK or emerging AI Kill Chain models enhances its efficacy. Download the original Lockheed Martin paper from their official site at https://www.lockheedmartin.com/en-us/capabilities/cyber/cyber-kill-chain.html for deeper insights, and invest in continuous training to fortify your defenses. Stay ahead in the digital battlefield—your cybersecurity posture depends on it.
References: Hutchins, E. M., Cloppert, M. J., & Amin, R. M. (2011). Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains. Lockheed Martin Corporation.

